Software innovation
The
Largest Global
Genesys Partner
200+ Dedicated Consultants
and Engineers Worldwide
Stop wasting time and money on technology. Let’s get started
Why Miratech?
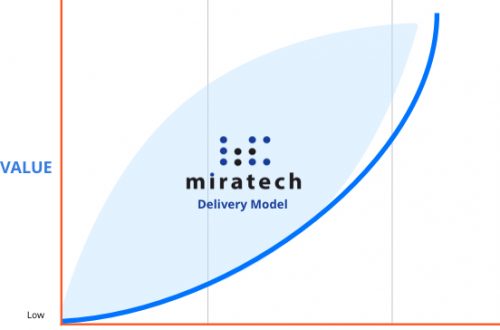
Miratech operates the largest Genesys competence center outside of Genesys, since 2000. Today, we employ over 200 dedicated Genesys consultants and engineers worldwide, supporting many of the largest installations at the most recognized world leaders in telecommunications, financial services, hospitality, retail and government. With 3+ million hours of installing, customizing and operating the Genesys platform we have a proven success record of beating schedules, budgets and accelerating ROI.
Why Miratech? Because our Relentless Performance guarantees your success.
Why Miratech? Because our Relentless Performance guarantees your success.
Why Miratech?
Because our Relentless Performance guarantees your success.
Because our Relentless Performance guarantees your success.
Two Thirds of All IT Projects Fail, So Why Do 99% of Ours Succeed?
Relentless Performance

Miratech’s Technical Excellence Guarantees a Successful
 Implementation
Implementation
Your team has worked endlessly on building the vision that will forever improve your customer experience. They’ve selected Genesys as the tool that will enable that vision. But what insures a successful Genesys implementation?
The technical excellence that comes from 20 years of developing the core code side-by-side the Genesys team.
The experience from supporting Genesys implementations worldwide, including the top 10.
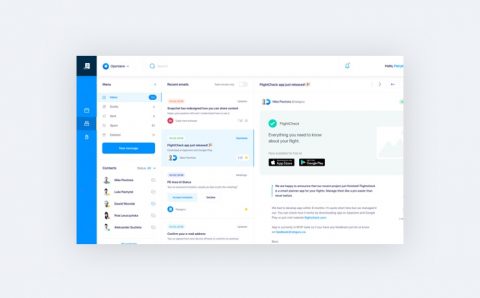
Miratech tools like Control CX™, which provide the transparency and accountability to track the features and tasks across the entire project, allowing management to view real-time data on budget, time to completion, and quality.
The leadership Miratech provides across teams to focus and achieve the results required.
Miratech supports complex Genesys PureEngage installations, as we thrive in the complexity most other companies are challenged with.
Contact us today to see how we can expedite your Genesys implementation to help your company achieve the customer experience vision your leadership has defined and your customers demand.
Contact us today to see how we can expedite your Genesys implementation to help your company achieve the customer experience vision your leadership has defined and your customers demand.
Your Success Begins With Miratech’s Relentless Performance.

Industries we Serve
For your very specific industry, we have highly-tailored IT solutions.
Engitech is the partner of choice for many of the world’s leading enterprises, SMEs and technology challengers. We help businesses elevate their value through custom software development, product design, QA and consultancy services.
Industries we Serve
For your very specific industry,
we have highly-tailored IT solutions.
1790
Happy clients
491
Finished projects
245
Skilled Experts
1090
Media Posts
Our Technology
Mitech – Top Software
Development Technology
Our strong passion to modern tech trends and best practices drive in the development of top-notch solutions that are perfectly tailored to provide high quality and affordable software outsourcing solutions to growing startup and enterprise companies in the world.

Blog
The Voice of Success From Vision Through Genesys Implementation
Understanding Public Cloud Security
Public Cloud, Hybrid Cloud and Multi-Tenancy Insights Public cloud security is often misunderstood. Did you know that public cloud solutions can be …
Ensure Operations Assurance and Migration Analysis for Seamless Evolution to Next-Generation Platforms
Understand ‘what’s next’ with Miratech’s Advanced Support Program If you’re a Genesys customer remaining on the existing Multicloud or Engage platforms, Miratech’s …
The CX Benefits of Gamification
Find out how gamification can transform your customer and employee engagement Gamification is not a new concept, however the number of applications …